Compromised Threat Assessment
Compromised Threat Assessment Methodology
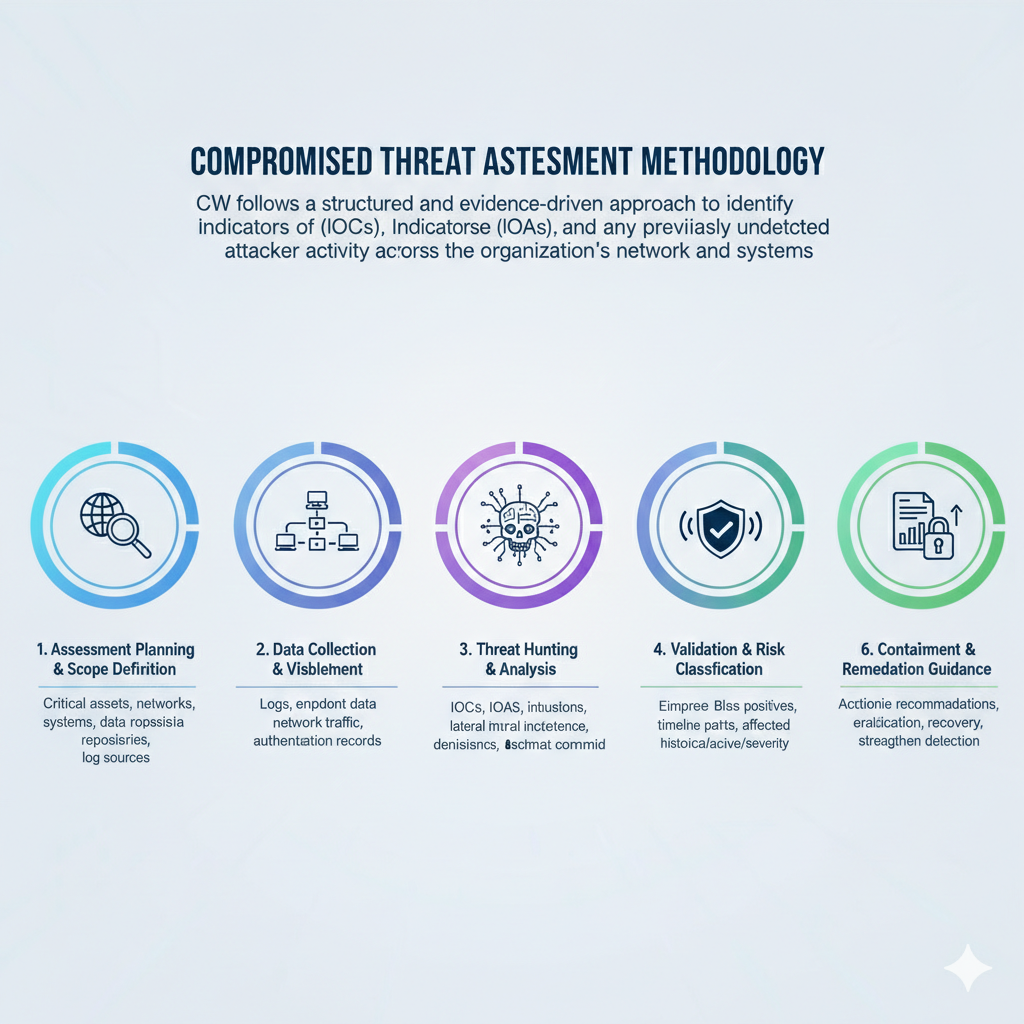
CW follows a structured and evidence-driven approach to identify Indicators of Compromise (IOCs), Indicators of Attack (IOAs), and any previously undetected attacker activity across the organization’s network and systems.
Our Structured Compromised Threat Assessment Approach
Ensuring proactive, thorough, and resilient threat management across your security landscape
1. Assessment Planning & Scope Definition
We begin by defining the assessment scope in collaboration with key stakeholders. This includes identifying critical assets, networks, systems, data repositories, and log sources. The objective is to ensure comprehensive visibility while minimizing operational impact.
2. Data Collection & Visibility Enablement
We collect and analyze relevant security telemetry, including logs, endpoint data, network traffic, authentication records, and security tool outputs. Where required, we enable additional visibility to ensure sufficient coverage for identifying malicious activity.
3. Threat Hunting & Analysis
Using threat intelligence, behavioral analytics, and forensic techniques, we proactively hunt for Indicators of Compromise (IOCs) and Indicators of Attack (IOAs). This phase focuses on identifying:
1. Evidence of successful or attempted intrusions
2. Lateral movement, persistence mechanisms, and privilege escalation
3. Dormant or ongoing attacker activity
4. Validation & Impact Assessment
All identified findings are validated to eliminate false positives. We assess the extent, timeline, and potential impact of any compromise, determining whether the threat is historical, active, or contained.
5. Reporting & Risk Classification
We deliver a comprehensive assessment report detailing identified artifacts of compromise, attack paths, affected assets, and risk severity. The report includes clear technical findings and executive-level summaries for informed decision-making.
6. Containment & Remediation Guidance
Where compromise indicators are identified, we provide actionable recommendations for containment, eradication, and recovery. This includes guidance to strengthen detection capabilities and prevent recurrence.
