Vulnerability Scanning & Penetration Testing / Social Engineering
Vulnerability Assessment & Penetration Testing Methodology
CW delivers comprehensive Vulnerability Assessment and Penetration Testing (VAPT) services through a structured, industry-aligned approach designed to identify, validate, and mitigate security risks across networks, systems, web applications, and mobile platforms.
Our delivery capability is supported by a global team of experienced, vetted security professionals who operate under strict ethical, confidentiality, and governance standards.
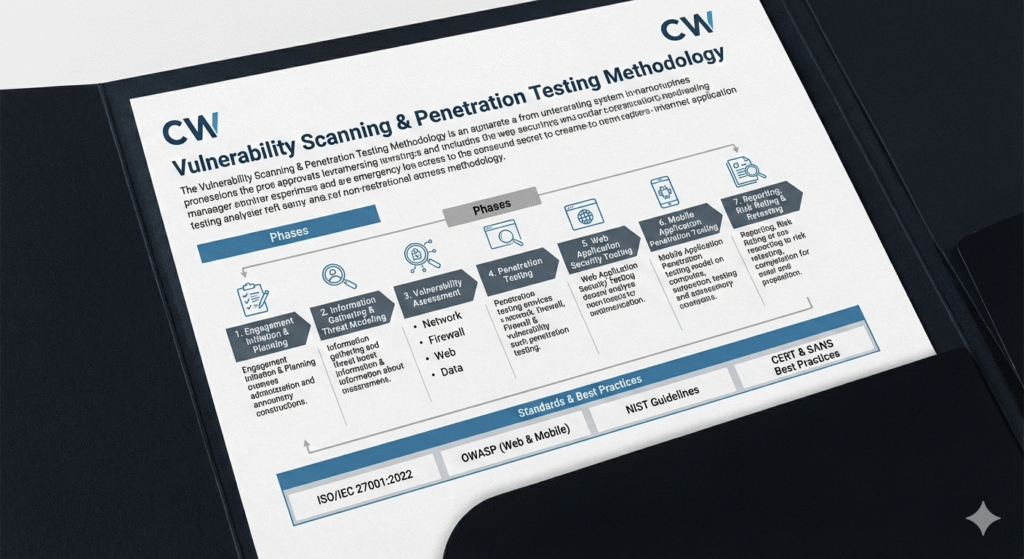
Our Structured Vulnerability Assessment & Penetration Testing (VAPT) Approach
Ensuring comprehensive, systematic, and fully aligned security risk identification and mitigation across your organization.
1. Engagement Initiation & Planning
We begin each engagement with a structured kickoff to align on objectives, scope, timelines, and success criteria. Key stakeholders are identified, testing boundaries are confirmed, and project governance is established to ensure clear communication and controlled execution.
2. Information Gathering & Threat Modeling
Our consultants perform a detailed review of architecture, applications, network diagrams, and configurations. We analyze the threat landscape, define attack scenarios, and validate assessment details in line with PTES and industry best practices. This phase forms the foundation for an effective and targeted assessment.
3. Vulnerability Assessment
We conduct systematic vulnerability scanning and analysis across in-scope infrastructure, servers, security controls, and applications. Using a combination of automated tools and manual techniques, we identify misconfigurations, exposed services, and known vulnerabilities that could be exploited by attackers.
Key focus areas include:
1. Network and server security
2. Firewall and perimeter controls
3. Web and application-layer vulnerabilities
4. Data leakage and misconfigurations
4. Penetration Testing
Where included, penetration testing extends vulnerability assessment by safely exploiting identified weaknesses to simulate real-world attack scenarios. Vulnerabilities are chained to assess the potential for lateral movement, privilege escalation, and system compromise, providing a realistic view of business risk.
5. Web Application Security Testing
Web applications are assessed using authenticated and unauthenticated access levels, aligned with the OWASP Testing Guide. Testing covers input validation, authentication and authorization, session management, data protection, injection flaws, access control weaknesses, and business logic abuse.
6. Mobile Application Penetration Testing
CW follows the OWASP Mobile Application Security Verification Standard (MASVS) and Testing Guide (MASTG). Our mobile testing includes attack surface mapping, automated and manual testing, exploitation of vulnerabilities, and backend API testing without requiring source code unless requested.
7. Reporting, Risk Rating & Retesting
All findings are validated and documented with clear risk ratings, business impact analysis, and actionable remediation guidance. Clients receive detailed technical reports and executive summaries. Retesting is performed to confirm effective remediation and reduce residual risk.
Standards & Best Practices
Our methodology aligns with globally recognized standards and frameworks, including:
1. ISO/IEC 27001:2022
2. OWASP (Web & Mobile)
3. NIST Guidelines
4. CERT & SANS Best Practices
Social Engineering Assessment
Our Social Engineering Assessment simulates real-world attack scenarios to evaluate how effectively your employees, processes, and controls withstand human-focused threats. We ethically test your organization under controlled conditions to identify behavioral risks before malicious actors exploit them.
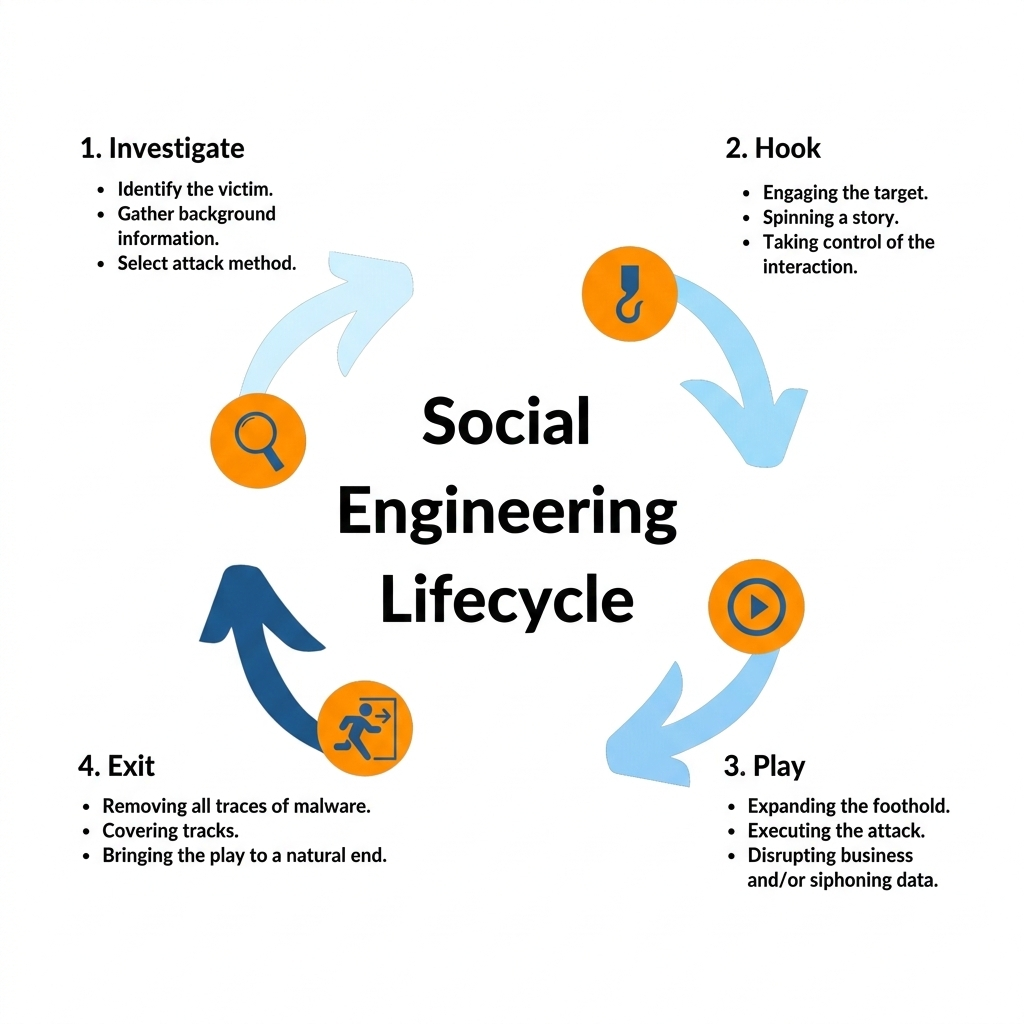
Our Structured Social Engineering Assessment Approach
We simulate how real attackers manipulate people not systems helping you reduce human risk before criminals do.
1. Planning & Authorization
We define scope, target groups, testing windows, and rules of engagement to ensure a controlled, ethical, and fully authorized assessment.
2. Threat Profiling (OSINT)
We analyze publicly available information to understand what attackers can learn about your organization without breaching any systems.
3. Scenario Design
We develop realistic attack simulations such as phishing emails, vishing calls, executive impersonation, vendor fraud, or physical access attempts.
4. Controlled Execution
We conduct simulated phishing, vishing, and messaging attacks while tracking employee responses without deploying malware, exploiting systems, or misusing data.
5. Detection & Risk Evaluation
We assess response times, reporting behavior, security control effectiveness, and overall business impact using risk-based analysis aligned with ISO 27001 and industry standards.
6. Reporting & Improvement Roadmap
You receive a board-ready executive summary, detailed findings, risk heat map, and a practical improvement roadmap including awareness and control enhancements
Compliance Alignment
This service supports:
1. ISO/IEC 27001
2. PCI DSS v4.0
3. SOC 2
4. Regulatory cyber security expectations
