Cybersecurity & Compliance
PCI DSS Compliance
CW teams help organizations achieve PCI DSS certification through our cybersecurity compliance services, delivered in three structured phases: scoping and gap assessment, remediation support, and final validation audit conducted by a qualified security assessor. The associated team has extensive experience delivering large-scale compliance engagements involving complex security controls and enterprise-level infrastructure.

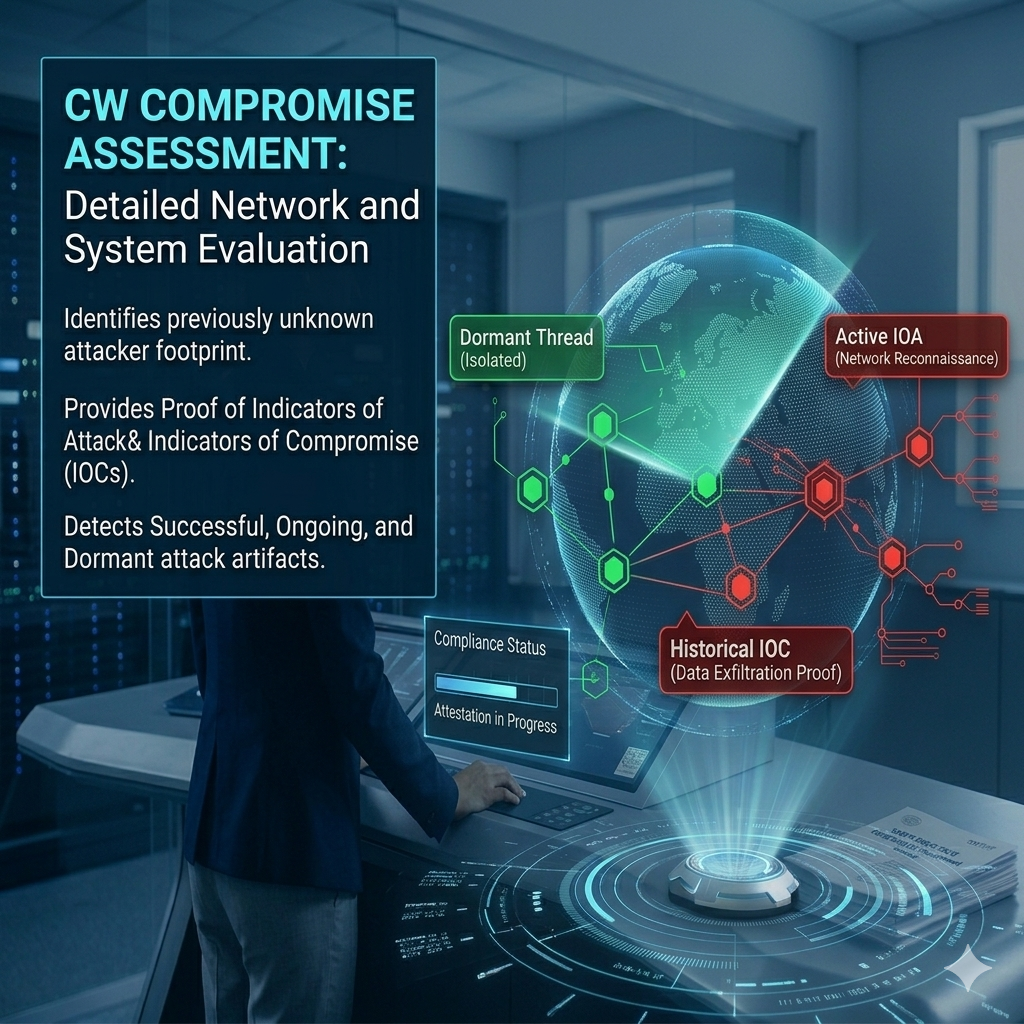
Compromised Threat Assessment
CW compromise assessment is an evaluation of the organization’s network and systems for artifacts of compromise and it provides proof of the previously unidentified footprint of an attacker or of the existence of Indicators of Attack (IOA) and Indicator of Compromise (IOCs), whether the attacker has been successful or not and whether an attack is ongoing or dormant.
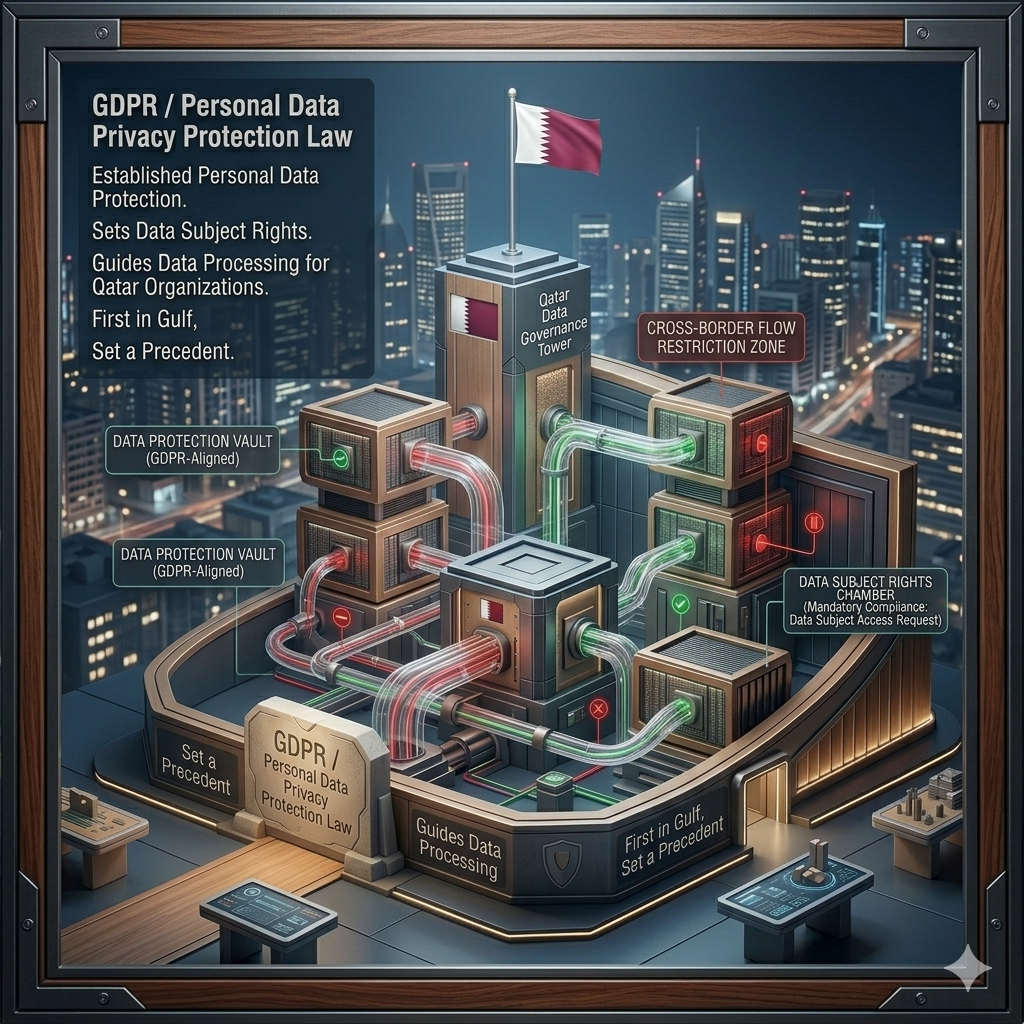
GDPR / Personal Data Privacy Protection Law
Qatar is the first Gulf country that has passed a national data privacy law and paved the way for all other Gulf countries to follow suit. In 2016, Qatar enacted Law No. 13 Concerning Personal Data Privacy Protection Law (the “PDPPL”). The PDPPL establishes a certain degree of personal data protection, provides data subject rights, and prescribes guidelines for organizations to process personal data within Qatar.

Vulnerability Scanning & Penetration Testing / Social Engineering
CW has certified penetration testers with proven track record of exploitation and social engineering. CW consultants utilizes proprietary as well as open-source tools for vulnerability reporting required as part of quarterly internal scans by PCI council and other regulatory authority such as central bank.
Cyber Security Health Check
A Cyber Security Health Check is a comprehensive assessment of an organization’s security posture to identify vulnerabilities, gaps, and risks across systems, networks, and processes. It involves evaluating current security controls, detecting potential threats, and recommending actionable measures to strengthen defenses. Our approach includes vulnerability scanning, configuration review, policy assessment, and risk analysis to ensure robust protection against cyber threats. Conducting regular Cyber Security Health Checks helps organizations maintain resilience, safeguard critical assets, and align with industry best practices and regulatory requirements.


Service Organization Control (SOC1 & SOC2) Readiness and Attestation
Our cybersecurity compliance services include complete end-to-end support for SOC readiness and attestation. This encompasses identifying Service Principals, defining the applicable Trust Services Criteria, and determining the scope for managed services, cloud environments, data centres, and other technology-driven operations. Through our services, CW evaluates existing controls, identifies gaps, and guides organizations through remediation, documentation, and evidence preparation to ensure a smooth and successful SOC attestation by an independent auditor.
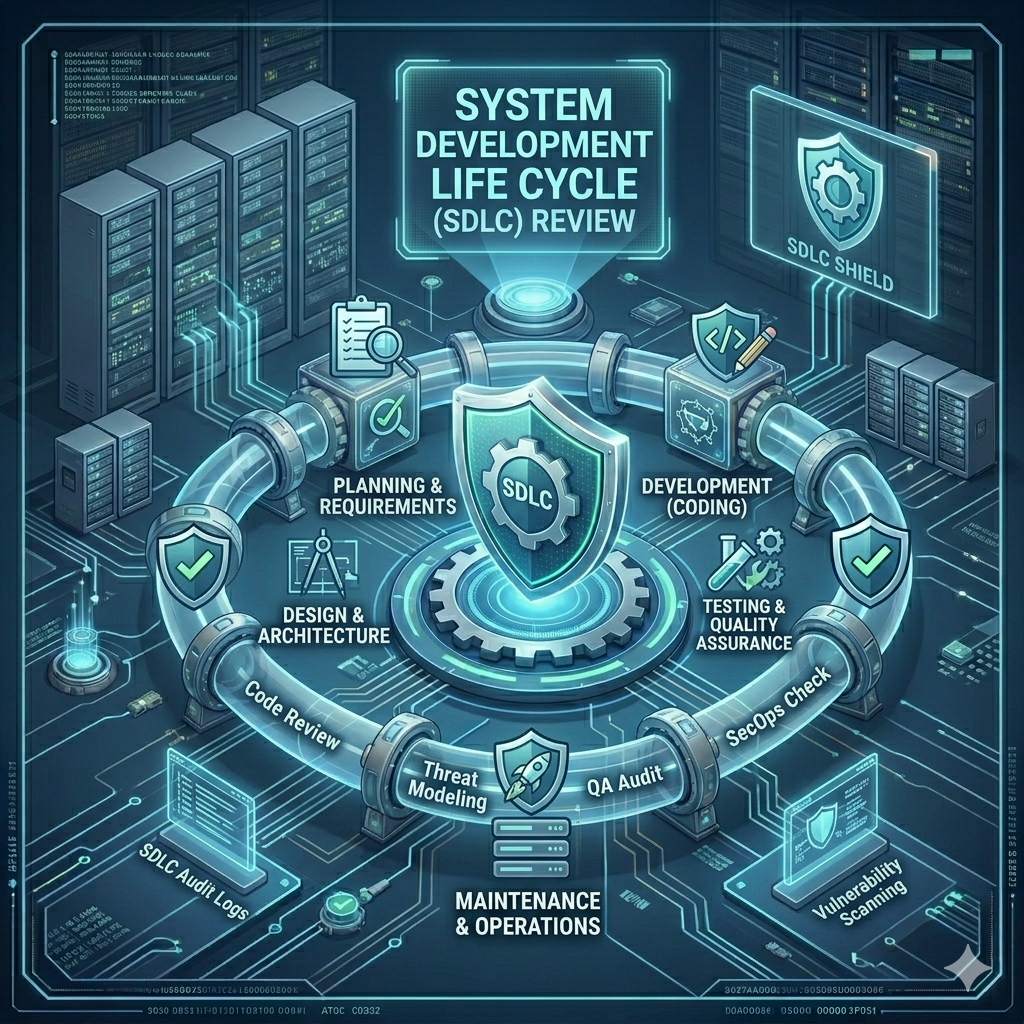
System Development Life Cycle (SDLC) Review
CW helps organization develop & implement SDLC into organization for planning, creating, testing, and deploying an information system. This includes training, procedure development and demo to developer and related staff.

PCI SSF Compliance
PCI Software Security Framework (SSF) compliance ensures that payment software meets the latest global security standards established by the PCI Security Standards Council. It focuses on safeguarding sensitive cardholder data through secure software design, development, and maintenance practices. Our approach includes rigorous testing, continuous monitoring, and implementation of best-in-class security controls to reduce risks. vulnerabilities and risks.
BCMS ISO22301 Implementation & Certification
CW helps organizations achieve Business Continuity Management (BCM) ISO/IEC22301 through its 3 step process gap assessment, formal assessment and certification with continued support for 3 years.


Telecommunication Regulatory Authority (TRA) Regulations
Compliance with TRA regulations ensures that organizations operating in the telecommunications sector adhere to the legal, technical, and security standards mandated by the national authority. It involves implementing robust governance frameworks, safeguarding customer data, maintaining network integrity, and following operational best practices. Our approach includes assessing regulatory compliance, identifying gaps, implementing corrective measures, and ensuring continuous monitoring. Adhering to TRA regulations not only mitigates legal and operational risks but also strengthens stakeholder trust and demonstrates commitment to industry standards.
11
Qatar Central Bank Regulations Implementation Support
CW has deep understanding of central bank regulation which provide cutting edge to our customer in putting what required keep the security and compliance intact. Central Bank (Qatar Central Bank) regulation covers the broad spectrum of services, and our line of services is according to the needs. Our reports has been shared and vouched by the regulator in past which give confidence and trust on the nature of work we carried out.
It is mandatory for all the Qatari Banking, Insurance and Financing Companies to follow Qatar Cyber Security framework. QCB Cyber Security framework includes many areas CW can help customers achieve them. This includes Cyber Security Risk Assessment | Cyber Security training | Regulatory compliance | Information Security Policies development | Penetration test etc. | Payment Services Regulations


ISMS ISO27001 Implementation & Certification
CW provides complete end-to-end support for ISMS ISO/IEC 27001 implementation and certification. This includes conducting the Risk Assessment, preparing the Statement of Applicability (SoA), and delivering awareness sessions to staff. To avoid any conflict of interest, ISO recommends that the consultant handling implementation should not perform the certification. Accordingly, CW will arrange an independent third-party consultant—Resource Inspections Canada Incorporated Pakistan Pvt. Ltd.—to carry out the validation and certification process.
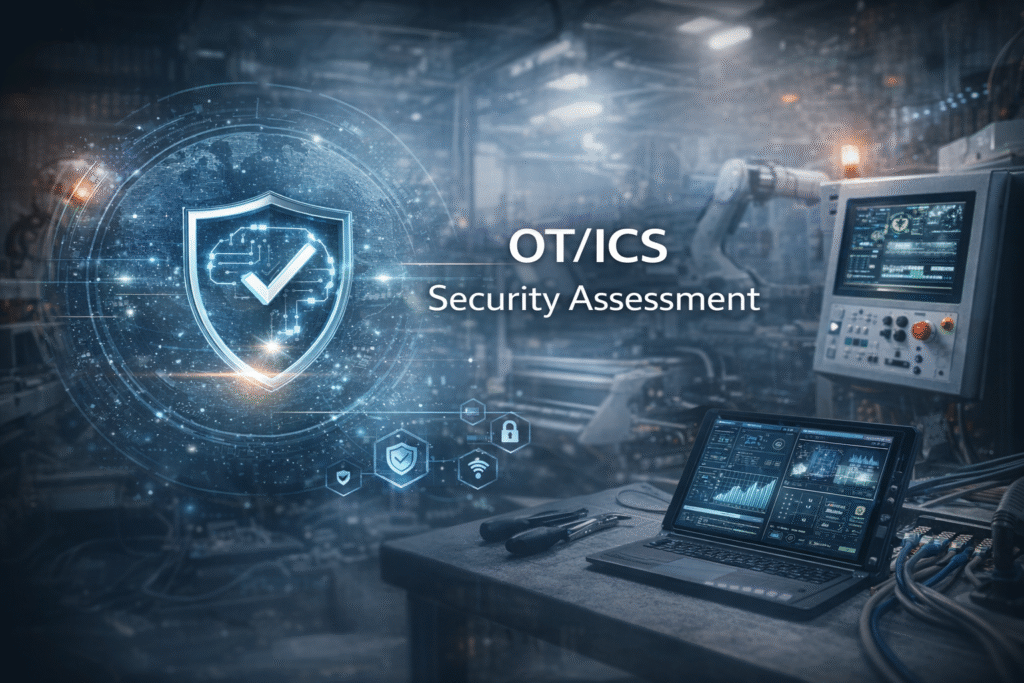
OT/ICS Security Assessment
Compliance Wing (CW) delivers specialized OT/ICS security services across the full industrial stack—from field devices to ERP systems. Our offerings include:
• OT/ICS Security Assessments
• Technical OT/ICS Audits
• OT/ICS Safety Studies
• OT/ICS Compliance Checks
Note: In Saudi Arabia, the National Cybersecurity Authority (NCA) mandates implementation of OTCC-1:2022, extending ECC-1:2018. ICS covers all systems and networks used to monitor and control industrial operations.

SWIFT CSCF Compliance
Our cybersecurity compliance services help financial institutions achieve SWIFT Customer Security Controls Framework (CSCF) compliance, ensuring adherence to mandatory security controls defined by SWIFT to protect the integrity of the global banking network. We focus on safeguarding messaging systems, preventing fraud, and reducing operational and cyber risks. Our approach includes assessing current controls, implementing required security measures, performing regular testing, and continuously monitoring compliance. Achieving SWIFT CSCF compliance through our cybersecurity compliance services not only strengthens the security of financial transactions but also demonstrates operational resilience, regulatory alignment, and a commitment to secure banking practices.
Payment Systems Security Assessment
Payment Systems Security Assessment is a comprehensive analysis of your ATMs and/or POS devices, designed to identify vulnerabilities that can be used by attackers for activities like unauthorized cash withdrawal, performing unauthorized transactions, obtaining your clients’ payment card data, or initiating denial of service. This service will uncover any vulnerabilities in your ATM/POS infrastructure that are exploitable by different forms of attack, outline the possible consequences of exploitation, evaluate the effectiveness of your existing security measures, and help you plan further actions to fix detected flaws and improve your security.


NIST Cybersecurity Framework
Compliance Wing implements the NIST CSF to move your organization beyond basic defense and toward true cyber resilience. We bridge the gap between technical complexity and strategic clarity by aligning your operations with the Identify, Protect, Detect, Respond, and Recover functions. By focusing on your specific risk landscape, we ensure that framework alignment is not just a one-time exercise, but a continuous, automated shield that hardens your infrastructure against sophisticated modern threats.
ISO 31000 Risk Management
Compliance Wing redefines risk management by embedding the ISO 31000 framework into your core decision-making processes. We move beyond “checkbox risk registers” to build a defensible environment where identifying, evaluating, and mitigating threats—aligned with global best practices—becomes a natural byproduct of your operational excellence. By aligning your technical reality with strategic risk oversight, we transform risk management from a static reporting burden into a proactive, resilient shield for your business growth.


Cloud Compliance (AWS / Azure / GCP)
Compliance Wing secures your digital transformation by integrating a Security-First mindset into your AWS, Azure, or GCP environments. We move beyond manual configuration checks to build cloud-native architectures where compliance is “baked in” and secure by design. By aligning your cloud infrastructure with global regulatory standards, we transform cloud governance from a complex hurdle into a continuous, automated shield that protects your data and enables your business to scale with total confidence.
HIPAA / HITRUST
Compliance Wing redefines healthcare data protection by making HIPAA and HITRUST compliance the natural byproduct of a hardened security posture. We move beyond administrative checklists to focus on the technical reality of safeguarding Protected Health Information (PHI) through multi-layered defenses and Zero-Trust architecture. By aligning your healthcare operations with stringent regulatory mandates, we transform patient data security from a liability concern into an ironclad shield that builds lasting trust with partners and patients alike.

IT Strategy Consulting
Compliance Wing bridges the gap between high-level business goals and technical execution through a Security-First IT Strategy. We move beyond standard consulting to design technology roadmaps where resilience and scalability are integrated from the start. By aligning your IT investments with your technical risk landscape, we transform your digital strategy from a cost center into a continuous, defensible shield that accelerates innovation while protecting your organization’s long-term reputation.
Security Architecture Review & Design
Compliance Wing ensures your systems are secure by blueprint, not by accident, through expert Architecture Review & Design. We move beyond perimeter-only defense to build Zero-Trust environments where every user, device, and data flow is verified and protected. By aligning your system architecture with the Technical Reality of your threat landscape, we transform your foundational security from a vulnerable patchwork into a robust, automated shield that naturally satisfies the most stringent compliance requirements.


IT Risk Assessment
Compliance Wing redefines the IT Risk Assessment by providing a deep-dive analysis of your “crown jewels” and the vulnerabilities that threaten them. We move beyond generic audits to uncover the specific technical gaps that expose your organization to breach and non-compliance. By aligning your current posture with a prioritized, risk-based roadmap, we transform your assessment from a static snapshot into the first step of a continuous, defensible shield that secures your future.
Information Security for Cloud ISO27017/2018
Compliance Wing secures your cloud-first evolution by embedding a Security-First mindset into the fabric of your virtualized infrastructure. We move beyond generic cloud security to provide specialized protection—aligned with ISO 27017 for cloud service controls and ISO 27018 for personal data protection in the cloud—ensuring your technical reality is both robust and defensible. By transforming complex cloud shared-responsibility models into a continuous, automated shield, we protect your tenant environments from leakage and ensure your reputation remains as scalable as your data.

KSA Regulations: NCA, SAMA & SDAIA
Compliance Wing navigates the complex regulatory environment of the Kingdom of Saudi Arabia, ensuring your organization is aligned with the NCA (National Cybersecurity Authority) frameworks, SAMA Cyber Security Framework, and SDAIA personal data protection laws. We embed a Security-First mindset into your architecture, providing tailored guidance that supports Vision 2030 and transforms localized data protection requirements into a robust, defensible foundation.
UAE Cybersecurity & Data Compliance
We navigate the complex regulatory landscape of the United Arab Emirates, specializing in NESA (IAS), Dubai ISR, and federal data protection laws. Compliance Wing ensures that your technical architecture meets the high standards of the UAE’s digital economy. We bridge the gap between regional mandates and technical execution, providing a secure foundation that protects both your data and your corporate reputation in the Gulf.


Oman Cybersecurity Compliance & Regulations
We provide tailored consultancy for the Sultanate of Oman, ensuring alignment with the Ministry of Transport, Communications and Information Technology (MTCIT) frameworks and the National Cybersecurity Centre (NCSC) standards. Compliance Wing helps Omani organizations protect their critical information infrastructure by implementing security designs that are culturally aware and technically superior, ensuring long-term stability in a rapidly evolving threat landscape.
National Compliance Service: SBP, SECP & NEPRA
Compliance Wing offers specialized support for Pakistan’s critical sectors, aligning your IT operations with the stringent frameworks of the State Bank of Pakistan (SBP), SECP, and NEPRA. Whether you are in Fintech, Energy, or Corporate sectors, we ensure your security posture is resilient against localized threats while remaining fully compliant with national oversight bodies. We turn “compliance burden” into “operational resilience.”

